AI: Cybersecurity's Ultimate Weapon or its Most Dangerous Vulnerability? The answer is both. 🛡️
The "AI Firewall" is no longer a futuristic concept; it's a rapidly evolving reality fundamentally reshaping our digital defenses. We're witnessing a dual evolution in how organizations are tackling the AI security challenge:
Key Takeaways
- Dedicated AI security solutions like Google VaultGemma and Akamai's Firewall for AI are emerging to protect AI models and applications.
- Cybersecurity giants are integrating AI security features into existing frameworks like XDR and SASE.
- "Shadow AI" and sophisticated AI-powered attacks are significant new threat vectors.
- AI is also a powerful defensive tool, enhancing Security Operations Centers (SOCs) and enabling proactive threat prevention.
- The "human firewall" and robust governance are critical to mitigating AI risks.

Google VaultGemma
An "AI privacy firewall" designed to secure training data, prevent model leakage, and establish truly secure AI architectures. Think end-to-end encryption + AI-driven anomaly detection.
Akamai's Firewall for AI
Specifically crafted to protect generative AI applications and Large Language Models (LLMs) from sophisticated threats like prompt injection, model theft, and data exfiltration. It's inspecting inputs and filtering outputs like never before.
2. AI Integration into Existing Frameworks:
Beyond standalone products, cybersecurity giants are embedding AI security capabilities directly into XDR, SASE, and traditional firewalls. Over $2.0 billion in M&A activity in 18 months underscores the industry's rapid move to secure enterprise AI through model scanning, prompt filtering, and agent sandboxing.
"AI is the new battleground for cybersecurity. The organizations that can harness its power for defense while mitigating its risks will be the ones that thrive in the digital age."
The Double-Edged Sword: AI as a Threat
But here's the stark reality: AI is also a formidable new threat vector.
- Shadow AI: 37% of employees are reportedly using unauthorized generative AI tools, creating massive data leak and compliance risks (hello, GDPR!).
- Sophisticated Attacks: Threat actors are leveraging AI for data poisoning, deepfake impersonation, and hyper-realistic phishing campaigns. No wonder 65% of IT leaders feel their current defenses are outdated. 🚨
AI: Our Most Potent Ally in Defense
Yet, AI is simultaneously our most potent ally. It's revolutionizing defense:
- Enhanced SOCs: Platforms like Stellar Cyber 6.1 equip teams with multi-layer AI for faster investigations, automated phishing triage, and AI-driven case summaries.
- Proactive Defense: Google's "Big Sleep" AI proactively prevented a zero-day vulnerability – a monumental shift towards predictive security.
- Unified Data Security: Microsoft Purview aims to unify data governance for the AI era, critical as 99% of organizations have faced sensitive data exposure via AI tools.
The Human Firewall
The stakes are higher than ever. Regulatory bodies are responding (e.g., CCPA amendments for AI), but the "human firewall" remains paramount. Employee education and robust governance frameworks are non-negotiable.
The future of cybersecurity is inherently AI-driven, and staying ahead means embracing its power while rigorously mitigating its risks. 🧠
Recent Posts
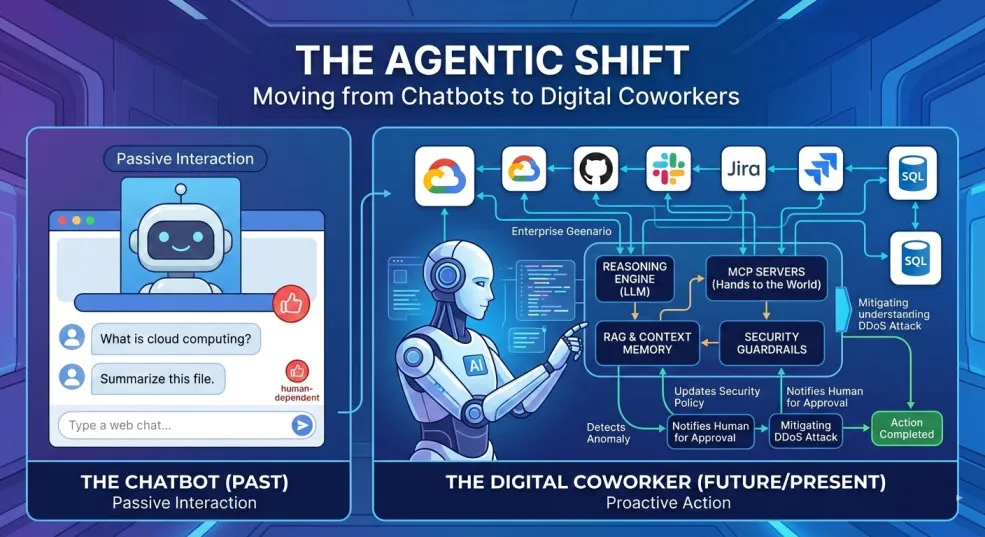
The Agentic Shift: Moving from Chatbots to Digital Coworkers
By 2026, enterprises are moving from AI chatbots that answer questions to digital coworkers that own outcomes across end-to-end workflows.

The Future of Agentic AI in Enterprise Applications
Why the next 3–6 months will define enterprise AI leadership — and how product and technology leaders can prepare for agentic systems that plan, decide, orchestrate, and execute.

Integration Modernization: An Enterprise Strategy for the Connected Enterprise
A Strategic framework for CIOs, CTOs, and enterprise architects to modernize integration, reduce risk, and unlock connected enterprise velocity.

Navigating the Future of AI Agents: MCP vs. A2A vs. ACP vs. ANP
A practical breakdown of the 4 key protocols shaping interoperable AI agents—what they do, where they fit, and how to choose (MCP, A2A, ACP, ANP).

AI 101: Your Gateway to the World of Large Language Models
A practical, non-fluffy guide to AI and Large Language Models (LLMs) for developers, CXOs, and AI leaders—what they are, how they work, when to use which model, and how to get reliable answers.

Google Maps for Your Code: Rescuing Architecture with the C4 Model
How the C4 model turns messy architecture diagrams into a clear, zoomable map of your systems—so teams can align, migrate, and evolve faster.
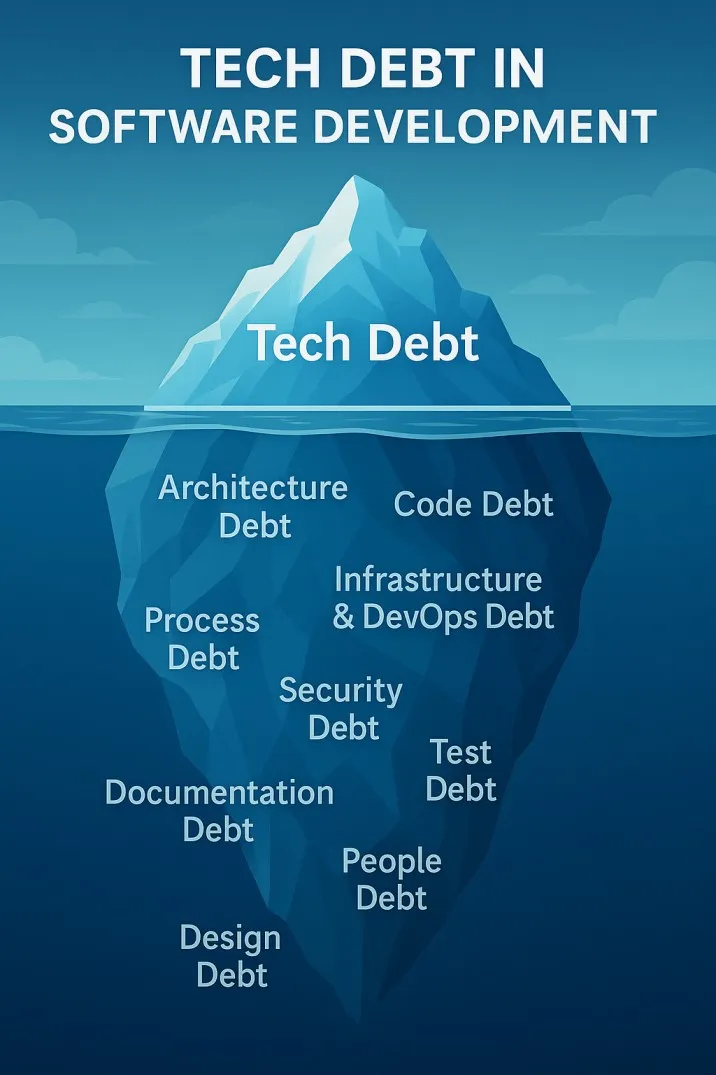
The Iceberg Beneath Your Code: Understanding Tech Debt in Software Development
Tech debt is the hidden iceberg beneath your codebase—slowing teams, inflating risk, and threatening outages. Here’s how to see it clearly and pay it down strategically.



