Integration Modernization: An Enterprise Strategy for the Connected Enterprise
A Strategic Framework for CIOs, CTOs, and Enterprise Architects
Executive Summary
Enterprise integration is no longer a back-office plumbing concern — it is the central nervous system of your digital business. Yet most organizations operate with integration architectures built incrementally over decades: brittle point-to-point connections, siloed ESBs, proprietary middleware, and ad-hoc file-based exchanges stitched together with institutional memory and good intentions. The result is a fragile, expensive, and innovation-blocking technical estate that quietly kills competitive velocity.

This document presents a structured, end-to-end strategy for Integration Modernization — the deliberate reimagination of how enterprise systems connect, communicate, and collaborate. It follows a five-phase consulting framework: Diagnose → Architect → Prioritize → Execute → Govern.
1. The Problem Statement: The Hidden Integration Debt Crisis
1.1 What Is Integration Debt?
Every enterprise accumulates integration debt — the compounding cost of poorly designed, undocumented, and unmaintained connections between systems. Unlike application technical debt, integration debt is invisible until a failure occurs. It hides in:
- Point-to-point spaghetti networks where N systems create N(N-1)/2 connections
- Monolithic ESBs (Enterprise Service Buses) that became single points of failure and organizational bottlenecks
- Hardcoded transformations buried in middleware configuration files no one understands
- Undocumented API contracts that break silently when upstream systems update
- Batch file transfers masquerading as integration in an era that demands real-time data flows
- Shadow integrations built by business units that bypassed IT — Salesforce → Google Sheets → SAP, anyone?
1.2 Why This Is a Strategic Problem, Not Just a Technical One
The business consequences of unaddressed integration debt are severe and compounding:
| Business Dimension | Impact of Integration Debt |
|---|---|
| Speed to Market | New product features take months because downstream system dependencies are unclear |
| Customer Experience | Data inconsistencies across CRM, billing, and support create frustrating customer journeys |
| Operational Efficiency | Manual rekeying of data between systems drives error rates and labor costs |
| Regulatory Compliance | Data lineage gaps make GDPR, SOX, and DPDP Act compliance audits painful |
| AI Readiness | Fragmented, siloed data prevents LLMs and ML models from accessing clean, unified context |
| M&A Agility | Acquiring or merging with another company takes 3–5x longer due to integration complexity |
| Developer Productivity | Engineers spend 30–40% of time on integration plumbing instead of business logic |
McKinsey Insight: Organizations that modernize integration infrastructure report 30–40% reduction in operational costs and dramatically accelerated innovation velocity compared to peers that do not.
2. Anatomy of the Problem: Why Enterprise Integration Breaks
2.1 The Evolution Trap
Most enterprise integration landscapes evolved through three eras, and organizations are frozen somewhere in the transition:
Era 1: Point-to-Point (1980s–2000s)
→ N systems × (N-1) connections → unmanageable complexity
Era 2: Enterprise Service Bus / SOA (2000s–2015)
→ Centralized but rigid; ESB became the "integration monolith"
Era 3: API-First / Event-Driven / Cloud-Native (2015–present)
→ Distributed, loosely coupled, observable — but requires deliberate governanceMost organizations have all three eras coexisting simultaneously, creating a heterogeneous landscape where no one person or team has full visibility.
2.2 The Six Integration Anti-Patterns
- "Call Me Directly" Anti-Pattern — System A calls System B's database directly, bypassing any API contract. A schema change in B silently breaks A.
- "Mega ESB" Anti-Pattern — All integrations are routed through a single ESB instance. One deployment window. One team. One bottleneck for every business unit.
- "File Drop" Anti-Pattern — Critical business data is exchanged via scheduled FTP/SFTP batch jobs. Real-time decisions are made on stale data.
- "Versioning? What's That?" Anti-Pattern — APIs have no versioning strategy. A change to an endpoint breaks 15 unknown consumers in production.
- "One Giant Transformer" Anti-Pattern — A single middleware component contains 10,000 lines of undocumented mapping logic. The developer who wrote it retired three years ago.
- "Shadow Integration" Anti-Pattern — Business teams use tools like Zapier, Power Automate, or manual exports to work around IT's slow integration delivery — creating ungoverned data flows outside security perimeters.
3. Real-World Case Studies: The Cost of Inaction
3.1 Hershey's — $150M Halloween Disaster (1999)
What Happened: Hershey Foods implemented three enterprise systems simultaneously — SAP ERP, Manugistics supply chain, and Siebel CRM — in an aggressive 30-month timeline to beat the Y2K deadline. The systems were not properly integrated or tested. When they went live in July 1999 — peak pre-Halloween order season — orders failed to flow between the systems.
The Integration Failure: The three vendor platforms (SAP, Manugistics, Siebel) were not validated for end-to-end data flow. Order data entered in Siebel did not reliably propagate to SAP's fulfillment engine, and supply chain signals from Manugistics were decoupled from actual warehouse execution.
Business Impact:
- Hershey could not fulfill $100M+ worth of orders for Kisses and Jolly Ranchers — products it physically had in warehouses
- Q3 1999 revenues dropped 12% year-over-year
- Operating income fell 19% in the same period
- Analyst confidence in the company took nine months to recover
Lesson: Integration is not a deployment afterthought. It is the critical path of any system modernization initiative.
3.2 Knight Capital Group — $440M Lost in 45 Minutes (2012)
What Happened: On August 1, 2012, Knight Capital deployed new trading software to seven of its eight servers for the NYSE's Retail Liquidity Program. One server — forgotten in the deployment process — ran old, deprecated code containing a defective function from a 2005 code reorganization that was never removed.
The Integration Failure: The new code triggered the dormant defective function on the unpatched server. The routing system could not recognize when orders had been filled, causing it to continuously re-route the same orders. Over 45 minutes, the system executed 4 million trades and accumulated $7 billion in unintended stock positions.
Business Impact:
- Knight Capital lost $440 million — exceeding its entire Q2 2012 revenue of $289M
- The firm was forced to sell itself within days to avoid bankruptcy
- The SEC charged Knight Capital with violations of market access rules
Lesson: Integration systems — especially those that span automated and manual deployment processes — require atomic, validated, and verified rollout procedures. A single inconsistent server state can be catastrophically expensive.
3.3 Target Canada — $7B Failure Driven by Data Integration (2015)
What Happened: Target launched 124 stores in Canada in 2013 with an SAP ECC ERP implementation on an "unrealistically tight" two-year timeline. The system was supposed to integrate merchandising, supply chain, pricing, and store operations.
The Integration Failure: Product master data was entered with errors at massive scale. Dimensions were entered in imperial units where metric was expected, product descriptions were wrong or missing, and costs were entered incorrectly. Because the ERP system's integration with supplier systems and the warehouse management system was not validated, these errors cascaded invisibly through the supply chain. Shelves were simultaneously overstocked with wrong products and understocked with high-demand items.
Business Impact:
- Target Canada accumulated $2.1 billion in losses in just two years
- Target announced the closure of all 133 Canadian stores in January 2015
- The parent company took a $5.4 billion write-down
- Described as a "gold standard case study in what retailers should not do"
Lesson: Data integration is not just about connectivity — it's about data contract governance, validation pipelines, and end-to-end observability across system boundaries.
3.4 NHS National Programme for IT — £10B Integration Catastrophe (UK, 2002–2011)
What Happened: The UK National Health Service launched the National Programme for IT (NPfIT) — envisioned as one of the world's largest public-sector IT programs — to create a unified patient record system across thousands of hospitals and GP practices.
The Integration Failure: The programme attempted to force diverse, independently-operated healthcare trusts — each with unique legacy clinical systems, data models, and workflows — into a single centralized integration architecture without adequate stakeholder buy-in, local customization support, or a phased integration model.
Business Impact:
- Initial budget: £12.4 billion; actual spend exceeded estimates by £10 billion
- The programme was formally abandoned in 2011 without delivering its core promises
- A House of Commons Public Accounts Committee report described it as "one of the worst and most expensive contrails of public money in the history of the public sector"
Lesson: A "big bang" centralized integration approach in a heterogeneous enterprise environment — especially one spanning hundreds of independent stakeholders — is an enterprise risk, not an enterprise strategy.
4. The Integration Modernization Framework
The following framework is structured as a five-phase consulting engagement model. Each phase has clear inputs, outputs, decisions, and success metrics.
┌─────────────┐ ┌─────────────┐ ┌─────────────┐ ┌─────────────┐ ┌─────────────┐
│ PHASE 1 │ → │ PHASE 2 │ → │ PHASE 3 │ → │ PHASE 4 │ → │ PHASE 5 │
│ DIAGNOSE │ │ ARCHITECT │ │ PRIORITIZE │ │ EXECUTE │ │ GOVERN │
│ │ │ │ │ │ │ │ │ │
│ Integration │ │ Target State│ │ Roadmap & │ │ Incremental │ │ Integration │
│ Landscape │ │ Architecture│ │ Wave Plan │ │ Delivery │ │ Center of │
│ Assessment │ │ Design │ │ │ │ │ │ Excellence │
└─────────────┘ └─────────────┘ └─────────────┘ └─────────────┘ └─────────────┘
Weeks 1–4 Weeks 4–8 Weeks 6–10 Months 3–18+ OngoingPhase 1: Diagnose — Integration Landscape Assessment
Objective: Establish a complete, honest picture of your current integration estate before designing any future state.
1.1 Integration Inventory Discovery
Run a structured discovery exercise across all business domains:
- Catalog all integrations — APIs, ESB flows, MQ queues, batch file transfers, database-level integrations, RPA bots, and shadow integrations
- Map ownership — Which team owns each integration? Is it documented? When was it last modified?
- Classify by criticality — Revenue-generating, compliance-related, operational, or informational
- Identify consumers — For each integration, how many downstream consumers depend on it? Are they known?
Tool Recommendation: Use a combination of API gateway logs, network traffic analysis, and stakeholder interviews. Tools like MuleSoft Anypoint, WSO2 API Manager, AWS API Gateway, or Apigee can help automate discovery if already in use.
1.2 Integration Health Scorecard
Evaluate each discovered integration against the following dimensions:
| Dimension | Questions to Answer | Risk Signal |
|---|---|---|
| Observability | Does it have logging, alerting, and tracing? | No monitoring = invisible failure |
| Documentation | Is there an up-to-date API contract or data flow diagram? | Undocumented = unmaintainable |
| Versioning | Is there a versioning strategy? How are breaking changes managed? | No versioning = fragile |
| Security | Is it authenticated? Is data encrypted in transit and at rest? | Unauthenticated = compliance risk |
| Error Handling | What happens on failure? Is there retry logic? Dead-letter queues? | No resilience = data loss |
| Latency Profile | Is it synchronous where async would suffice? | Wrong pattern = performance bottleneck |
| Ownership | Is there a named team and on-call contact? | No ownership = orphaned integration |
1.3 Categorize the Integration Portfolio
Segment your integration portfolio into four quadrants:
HIGH BUSINESS VALUE
│
┌────────────────────┼────────────────────┐
│ MODERNIZE │ INVEST & SCALE │
│ (Refactor now) │ (Priority work) │
LOW ─────┼────────────────────┼──────────────────── HIGH
TECH │ │ TECH
DEBT │ RETIRE │ WATCH DEBT
│ (Decommission) │ (Monitor) │
└────────────────────┼────────────────────┘
│
LOW BUSINESS VALUEDeliverable: Integration Landscape Assessment Report with portfolio heat map, technical debt score, and top-10 risk-ranked integrations.
Phase 2: Architect — Target State Design
Objective: Design a future-state integration architecture that is loosely coupled, observable, secure, and composable — without requiring a full "big bang" replacement.
2.1 Choose Your Integration Paradigm
Modern enterprise integration is not a single pattern. The right architecture is a deliberate combination of paradigms, each applied where it is most appropriate:
Paradigm 1: API-Led Connectivity (Request-Response)
Best For: Synchronous interactions, user-facing experiences, B2B/B2C integrations
Organizes APIs into three reusable layers:
- System APIs — Thin wrappers that expose raw capabilities of backend systems (SAP, Salesforce, Oracle, legacy mainframes) in a standardized protocol
- Process APIs — Orchestrate System APIs to implement business processes (e.g., "Create Order" calls Customer API + Inventory API + Pricing API)
- Experience APIs — Tailored for specific consumer channels (mobile app, partner portal, internal dashboard) combining Process APIs with UI-specific logic
[Mobile App] [Web Portal] [Partner API]
│ │ │
└───────────────┼─────────────┘
EXPERIENCE LAYER
│
┌────────────┼────────────┐
│ │ │
ORDER CUSTOMER PRICING
PROCESS PROCESS PROCESS
│ │ │
┌────┼───┐ ┌───┼──┐ ┌───┼──┐
SAP WMS OMS SFDC MDM CPQ ERP TAXParadigm 2: Event-Driven Architecture (Async / Pub-Sub)
Best For: High-volume, decoupled, real-time data flows between internal systems (A2A)
Key concepts:
- Event Producers publish domain events (e.g.,
OrderCreated,InventoryUpdated,PaymentProcessed) to a message broker - Event Consumers subscribe to relevant event topics and react asynchronously
- Message Broker (Apache Kafka, AWS EventBridge, Google Pub/Sub, Azure Service Bus) provides durability, replay, and fan-out
When to use EDA over API-Led:
| Scenario | API-Led | EDA |
|---|---|---|
| User requests a product page | ✅ Synchronous response needed | ❌ |
| Order placed → trigger fulfillment, loyalty, billing, analytics | ❌ Tight coupling | ✅ Pub-Sub fan-out |
| Real-time inventory sync across 50 stores | ❌ Poll-based is stale | ✅ Event stream |
| Partner B2B data exchange | ✅ Clear request-response contract | ❌ |
Paradigm 3: Data Integration & Streaming
Best For: Analytics, AI/ML data pipelines, regulatory reporting
- ETL/ELT pipelines for batch data consolidation into data warehouses (BigQuery, Snowflake, Redshift)
- CDC (Change Data Capture) tools like Debezium to stream database changes as events without application-layer coupling
- Data mesh architecture — federated ownership of data products with centralized discoverability
Paradigm 4: Hybrid Integration Platform (HIP)
Most enterprises cannot move everything to the cloud at once. A Hybrid Integration Platform:
- Combines cloud-native iPaaS (MuleSoft, Azure Integration Services, AWS AppFabric, Google Apigee) with on-premise connectors
- Uses secure tunnels, VPNs, or integration gateways to bridge legacy on-premise systems with cloud-native services
- Preserves existing investments while enabling incremental modernization
2.2 The Target Architecture Principles
Define and ratify these principles before writing a single line of architecture:
- API-First: Every capability is exposed through a documented, versioned API before internal consumption
- Loose Coupling: No service should know the internal implementation of another; only its published contract
- Event as a First-Class Citizen: State changes in any domain system produce events consumable by any authorized subscriber
- Observability by Default: Every integration has distributed tracing, structured logging, and alerting before it goes to production
- Security by Design: All APIs are authenticated (OAuth 2.0 / JWT), authorized (RBAC/ABAC), and encrypted (TLS 1.3 minimum)
- Fail Gracefully: Every integration implements retry logic, circuit breakers, and dead-letter queues
- Own Your Contracts: API contracts (OpenAPI 3.x, AsyncAPI) are version-controlled, peer-reviewed, and published to a developer portal
2.3 Reference Architecture
┌─────────────────────────────────┐
│ DEVELOPER PORTAL │
│ (API Catalog, Docs, Onboarding) │
└─────────────────────────────────┘
│
┌─────────────────────────────────────────────────────────────────┐
│ API GATEWAY LAYER │
│ (Auth, Rate Limiting, Routing, SSL Termination, Analytics) │
└─────────────────────────────────────────────────────────────────┘
│ │ │
┌──────┴──────┐ ┌──────┴──────┐ ┌──────┴──────┐
│ EXPERIENCE │ │ PROCESS │ │ SYSTEM │
│ APIs │ │ APIs │ │ APIs │
│ (Channel- │ │ (Business │ │ (Backend │
│ Specific) │ │ Workflows) │ │ Wrappers) │
└─────────────┘ └─────────────┘ └─────────────┘
│
┌───────────────────────┴───────────────────────┐
│ EVENT BUS / MESSAGE BROKER │
│ (Kafka / Pub-Sub / Service Bus) │
└───────────────────────────────────────────────┘
│ │ │ │
┌─────┴──┐ ┌────┴───┐ ┌───┴────┐ ┌──┴─────┐
│ ERP │ │ CRM │ │ WMS │ │ Legacy │
│ (SAP) │ │(SFDC) │ │ │ │Mainframe│
└────────┘ └────────┘ └────────┘ └────────┘Phase 3: Prioritize — The Integration Modernization Roadmap
Objective: Sequence the modernization work to maximize value, minimize risk, and demonstrate early wins.
3.1 The Wave Planning Model
Avoid the "big bang" at all costs. Structure delivery in three waves:
Wave 1 — Stabilize & Protect (Months 1–4)
Goal: Stop the bleeding. Fix critical risks before building anything new.
- Implement monitoring and alerting on all Tier 1 integrations (if not already in place)
- Document and create runbooks for the top-10 highest-risk, undocumented integrations
- Retire integrations confirmed as unused (ROT analysis — Redundant, Obsolete, Trivial)
- Stand up API Gateway as a façade for externally-consumed APIs (immediate security win)
- Establish the Integration Center of Excellence (ICoE) team and governance charter
Key Metric: Reduce P1 integration incidents by 30% within 90 days
Wave 2 — Modernize Core Domains (Months 4–12)
Goal: Rebuild foundational integrations using the target architecture, domain by domain.
Prioritize domains by this scoring matrix:
| Domain | Business Value | Technical Debt | AI/Data Readiness Need | Modernization Priority |
|---|---|---|---|---|
| Customer (CRM ↔ Marketing ↔ Support) | High | High | High | 1st |
| Order-to-Cash (OMS ↔ ERP ↔ Payment) | High | Medium | High | 2nd |
| Supply Chain (WMS ↔ ERP ↔ Logistics) | High | High | Medium | 3rd |
| HR & Employee Systems | Medium | Low | Low | 4th |
| Finance & Compliance | High | Medium | High | 5th |
For each domain, apply the Strangler Fig Pattern:
- Place the API Gateway as a façade in front of the legacy system
- Build the new integration layer in parallel behind the façade
- Gradually shift traffic from the legacy path to the new path
- Decommission the legacy integration when traffic is fully migrated
This approach allows existing consumers to continue operating uninterrupted while the modernization occurs beneath the surface.
Wave 3 — Scale & Innovate (Months 12–24+)
Goal: Enable business capabilities that were previously impossible.
- Deploy event-driven integration for real-time business intelligence and AI data pipelines
- Open internal APIs to external partners via a governed developer portal
- Implement API monetization for strategic ecosystem plays
- Enable self-service integration for business teams (governed iPaaS with guardrails)
- Feed clean, integrated data into LLM and ML pipelines for AI-powered experiences
3.2 Prioritization Scoring Model
Score each integration modernization candidate on five dimensions (1–5 scale):
Priority Score = (Business Value × 2) + Risk Reduction + Developer Velocity + AI/Data Readiness + Regulatory Compliance| Integration | Business Value (×2) | Risk Reduction | Dev Velocity | AI Readiness | Compliance | Total |
|---|---|---|---|---|---|---|
| CRM → ERP Order Sync | 10 | 4 | 4 | 5 | 3 | 26 |
| Legacy FTP Batch → Event | 6 | 5 | 3 | 4 | 5 | 23 |
| Partner EDI → REST API | 8 | 4 | 5 | 3 | 4 | 24 |
| Internal HR → Payroll | 4 | 3 | 2 | 2 | 5 | 16 |
Higher scores go first.
Phase 4: Execute — Delivery Playbook
Objective: Deliver integration modernization iteratively, with quality gates, validated by real consumers.
4.1 The Integration Delivery Lifecycle
Every integration modernization initiative must follow this lifecycle:
DISCOVER → DESIGN → DEVELOP → TEST → DEPLOY → MONITOR → RETIREDISCOVER
- Identify all current consumers of the integration being modernized
- Document current payload schema, error behaviors, latency SLAs, and edge cases
- Conduct consumer interviews: "What does this integration do for your system that nothing else can?"
DESIGN
- Define the API contract (OpenAPI 3.x for REST; AsyncAPI for events) before writing code
- Conduct a contract review with all consumer teams
- Define error taxonomy: what error codes are returned, when, and what consumers should do
- Design for idempotency — especially for event consumers and retry scenarios
DEVELOP
- Build integration components as independently deployable units (not monolithic transformation blobs)
- Use infrastructure-as-code for all integration runtime infrastructure
- Implement circuit breakers, retry with exponential backoff, and dead-letter queues from day one
- Enforce API contract testing (Pact, Postman Contract Tests) in CI/CD pipelines
TEST
- Unit Tests: Individual transformation logic and mapping
- Contract Tests: Producer-consumer API contract validation (prevents the Knight Capital scenario)
- Integration Tests: End-to-end flow validation in a staging environment
- Performance Tests: Load test at 3–5× expected peak traffic before production
- Chaos Engineering: Introduce failures (network partitions, service unavailability) to validate resilience
DEPLOY
- Use canary or blue-green deployment for all integration changes
- Never deploy to all consumers simultaneously (avoid the Knight Capital single-server mistake)
- Require feature flags for enabling new integration behavior
- Maintain a deployment runbook and rollback procedure for every release
MONITOR
- Define SLOs for every integration: availability (e.g., 99.9%), latency (e.g., p99 < 500ms), error rate (e.g., < 0.1%)
- Instrument with distributed tracing (OpenTelemetry) to trace requests across system boundaries
- Create integration-specific dashboards with consumer impact visibility
- Set up automated anomaly detection — do not rely on consumer teams to report failures
RETIRE
- Formally communicate deprecation timelines (minimum 6 months for internal; 12 months for external)
- Track consumer migration using gateway analytics
- Only decommission after all consumers have migrated and zero traffic confirmed
4.2 The Strangler Fig in Practice
Here is a concrete example of applying the Strangler Fig Pattern to a legacy SAP-to-CRM integration:
Before (Legacy State):
Salesforce CRM ──direct BAPI call──→ SAP ERP
(fragile, no auth, no retry, no monitoring)Step 1 — Place the Façade:
Salesforce CRM ──REST API──→ [API Gateway Façade] ──BAPI call──→ SAP ERP
(now: auth, rate limiting, logging — but SAP integration unchanged)Step 2 — Build New Integration Layer:
Salesforce CRM ──REST API──→ [API Gateway] ──→ [New System API] ──→ SAP ERP
↘ ──BAPI call──→ SAP ERP (legacy path, parallel)Step 3 — Shift Traffic (Canary):
Salesforce CRM ──REST API──→ [API Gateway] ──10% traffic──→ [New System API] ──→ SAP ERP
──90% traffic──→ [Legacy BAPI call] ──→ SAP ERPStep 4 — Full Migration & Decommission:
Salesforce CRM ──REST API──→ [API Gateway] ──→ [New System API] ──→ SAP ERP
(legacy BAPI call retired; full observability, circuit breaker, retry)4.3 Accelerator: AI-Assisted Integration Development
Modern AI tools significantly accelerate integration modernization:
- Legacy Code Understanding: Use LLMs (Claude, GitHub Copilot) to reverse-engineer undocumented transformation logic in XSLT, COBOL, or proprietary mapping languages
- API Contract Generation: Generate OpenAPI specifications from existing endpoint behavior using traffic capture tools
- Test Generation: Use AI to generate edge-case test scenarios for data transformation logic
- Documentation: Auto-generate integration runbooks and data dictionaries from code and API specs
- Anomaly Detection: Apply ML models to integration traffic patterns to detect degradation before SLO breach
Note for Telecom Context: In a 15,000-developer enterprise, AI-assisted integration tooling embedded in the developer SDK can reduce new integration delivery time from weeks to days, while ensuring adherence to integration standards by design.
Phase 5: Govern — The Integration Center of Excellence (ICoE)
Objective: Establish the organizational capability to sustain integration quality, prevent new integration debt, and continuously evolve the integration platform.
5.1 The Integration Center of Excellence Model
The ICoE is not a centralized bottleneck — it is an enabling function that sets standards, builds platforms, and provides guardrails so product teams can move fast safely.
ICoE Team Structure:
┌───────────────────────────────┐
│ INTEGRATION CENTER OF │
│ EXCELLENCE (ICoE) │
└───────────────────────────────┘
┌──────────────┐ ┌──────────────┐ ┌──────────────┐ ┌──────────────┐
│ Integration │ │ API │ │ Data │ │ Developer │
│ Architects │ │ Governance │ │ Integration │ │ Experience │
│ │ │ & Standards │ │ & Pipelines │ │ & Portal │
└──────────────┘ └──────────────┘ └──────────────┘ └──────────────┘ICoE Responsibilities:
| Responsibility | Description |
|---|---|
| Platform Engineering | Build and operate the integration platform (API gateway, message broker, iPaaS) |
| Standards & Patterns | Define reusable integration patterns, API naming conventions, error taxonomies |
| Developer Portal | Maintain the API catalog, onboarding guides, and SDK/connector library |
| Governance Enforcement | API design reviews, contract testing mandates, deprecation management |
| Integration Health | Monitor platform health, SLO compliance, and integration debt levels |
| Education | Train engineering teams on integration patterns, best practices, and tools |
5.2 Integration Governance Model: The Three-Tier Policy
Tier 1 — Non-Negotiable (Automated Enforcement):
- All APIs must have an OpenAPI 3.x spec checked into version control
- All APIs must be registered in the API gateway before internal or external consumption
- All APIs must implement OAuth 2.0 authentication (no API keys for production systems)
- CI/CD pipelines block deployment if contract tests fail
Tier 2 — Required with Exception Process:
- APIs must use semantic versioning (major.minor.patch)
- Breaking changes require 6-month deprecation notice with consumer migration tracking
- All integrations must have a defined SLO and monitoring dashboard
- Event schemas must be registered in the Schema Registry
Tier 3 — Recommended Best Practices:
- Prefer asynchronous over synchronous patterns for non-user-facing integrations
- Use idempotency keys for all write operations
- Implement correlation IDs for distributed tracing across integration chains
5.3 The Integration Debt Dashboard
Track integration modernization progress using these KPIs:
| KPI | Target | Measurement |
|---|---|---|
| % of integrations with monitoring | 100% (Tier 1) | API Gateway + Observability Platform |
| % of APIs with published OpenAPI spec | 100% | API Registry |
| Integration P1 incident rate | < 2/month | Incident Management System |
| Mean Time to Detect (MTTD) | < 5 minutes | Observability Platform |
| Mean Time to Recover (MTTR) | < 30 minutes | Incident Management |
| % of legacy batch integrations retired | Progress by quarter | Portfolio tracker |
| Developer onboarding time (new integration) | < 2 days | Developer portal analytics |
| API reuse rate | > 40% of new integrations use existing APIs | API Gateway analytics |
5.4 Sustaining the Modernization: Avoiding Reaccumulation of Debt
Integration modernization is not a one-time project. Without sustained governance, new debt accumulates within 18–24 months. Prevent this by:
- Make the right way the easy way — Provide templates, scaffolding, and SDKs that make standard integration patterns faster to build than custom solutions
- Shift-left governance — Review API contracts at design time, not after code is written
- Integration fitness functions — Automated architectural tests that continuously verify integration health (e.g., "no integration shall have a dependency on another integration's database")
- Quarterly architecture reviews — Review the integration portfolio health score every quarter and prioritize debt reduction in the planning cycle
- FinOps for integration — Track the cost of operating each integration; unmeasured cost is unjustified cost
6. Common Failure Modes to Avoid
Even well-intentioned integration modernization programs fail. The top failure patterns:
| Failure Mode | Description | Prevention |
|---|---|---|
| "Big Bang" Temptation | Attempting to replace all integrations simultaneously | Strict wave planning; Strangler Fig for all migrations |
| Governance Theater | Standards documented but not enforced | Automate enforcement in CI/CD; remove human gates for known rules |
| Platform Without Adoption | Building a beautiful integration platform nobody uses | Developer experience is a product; invest in SDKs, docs, and onboarding |
| Ignoring the Shadow | Shadow integrations continue to grow outside the modernized landscape | Mandate integration platform use through policy; make it easy |
| Data Quality Neglect | Modern integration routes corrupt or inconsistent data at high speed | Implement data contract validation at every system boundary |
| Observability as Afterthought | Monitoring added after go-live, when incidents are already occurring | Observability is a deployment gate, not a post-launch task |
| Stakeholder Fatigue | Long modernization programs lose executive sponsorship | Deliver business value in Wave 1; celebrate and communicate wins loudly |
7. Technology Landscape Reference
Select tools appropriate to your existing platform investments:
| Category | Options | Notes |
|---|---|---|
| API Gateway | Kong, AWS API Gateway, Apigee (GCP), Azure APIM, MuleSoft | Select based on cloud platform alignment |
| iPaaS / Integration Platform | MuleSoft Anypoint, Azure Integration Services, AWS AppFabric, Boomi, Workato | Evaluate based on connector library and governance capabilities |
| Message Broker / Event Streaming | Apache Kafka, AWS EventBridge + SQS, Google Pub/Sub, Azure Service Bus | Kafka for high-throughput streaming; managed services for lower operational overhead |
| API Design & Registry | SwaggerHub, Stoplight, Apicurio, Backstage | Backstage for developer portal; Apicurio for schema registry |
| Observability | Datadog, Dynatrace, OpenTelemetry + Grafana, Google Cloud Monitoring | OpenTelemetry as vendor-neutral instrumentation standard |
| Data Integration | Debezium (CDC), dbt, Apache Airflow, Fivetran, Google Dataflow | Choose based on data warehouse platform |
| Contract Testing | Pact, Postman, Specmatic | Pact for consumer-driven contract testing |
| Service Mesh | Istio, Linkerd, AWS App Mesh | For internal service-to-service communication governance |
8. Executive Commitment: The Business Case
8.1 The Cost of Doing Nothing
Frame the business case around the cost of inaction, not just the benefit of action:
- Incident cost: Each P1 integration outage costs an average enterprise $300,000–$500,000 in direct and indirect losses
- Velocity tax: Engineering teams spend 30–40% of development time on integration plumbing — this is measurable and recoverable
- AI opportunity cost: Every quarter that data remains siloed is a quarter where AI initiatives deliver less value than competitors who have unified their data
- Compliance exposure: GDPR, SOX, DPDP Act fines for data mishandling enabled by ungoverned integrations can reach 4% of global annual turnover
8.2 The Investment and Return Model
Typical Investment Profile (Mid-Large Enterprise, 18-month program):
| Phase | Activities | Indicative Investment |
|---|---|---|
| Wave 1: Stabilize | ICoE setup, monitoring, documentation | Low (primarily people) |
| Wave 2: Modernize | Platform, development, migration | Moderate-High |
| Wave 3: Innovate | Event-driven, AI pipelines, partner portal | Moderate (incremental) |
Expected Returns (18–36 month horizon):
- 30–40% reduction in integration-related operational costs
- 50–60% reduction in time-to-integrate for new systems
- 3–5× improvement in developer productivity for integration tasks
- Measurable reduction in P1 incident frequency and MTTR
- AI readiness: Clean, governed data flows enabling LLM and ML model deployment
9. The C-Suite Narrative: Framing Integration Modernization as a Board Priority
Integration modernization is not a technology upgrade — it is a business capability investment. Frame it for leadership as:
"We are rebuilding the highways between our business systems. Today, our data flows through dirt roads with no traffic signals, no GPS, and no accident reporting. We are replacing them with a monitored, governed, and high-speed data infrastructure — so that every new digital initiative we launch can move at the speed of the business, not the speed of the slowest legacy integration."
The Three Board-Level Imperatives:
- Competitive Agility: Integrated enterprises launch new products in weeks. Siloed enterprises take quarters. This is not sustainable.
- AI Monetization: Every AI strategy depends on clean, real-time, unified data. Integration modernization is the prerequisite to every AI investment on the roadmap.
- Risk Management: The Knight Capital ($440M in 45 minutes), Hershey ($150M in one quarter), and Target Canada ($7B total loss) failures were all, at their root, integration governance failures. This is a category of enterprise risk that boards must treat with the same seriousness as cybersecurity.
Conclusion: The Integrated Enterprise Is the Competitive Enterprise
Integration modernization is not a destination — it is a discipline. The organizations that will lead their industries in the next decade are those that treat their integration estate as a strategic asset, invest in its governance, and build the organizational capability to evolve it continuously.
The framework presented here — Diagnose → Architect → Prioritize → Execute → Govern — is designed to be pragmatic, incremental, and value-driven. It does not require a multi-year "rip-and-replace" program. It requires deliberate sequencing, strong governance, and unwavering executive commitment to the principle that connected systems create connected experiences — and connected experiences are what customers, partners, and developers choose to build their futures with.
Strategy authored using a McKinsey-aligned consulting framework. Data references include Gartner, Forrester, Deloitte, McKinsey & Company, and primary case research from Hershey Foods (1999), Knight Capital Group (2012), Target Canada (2015), and UK NHS NPfIT (2002–2011).
Recent Posts
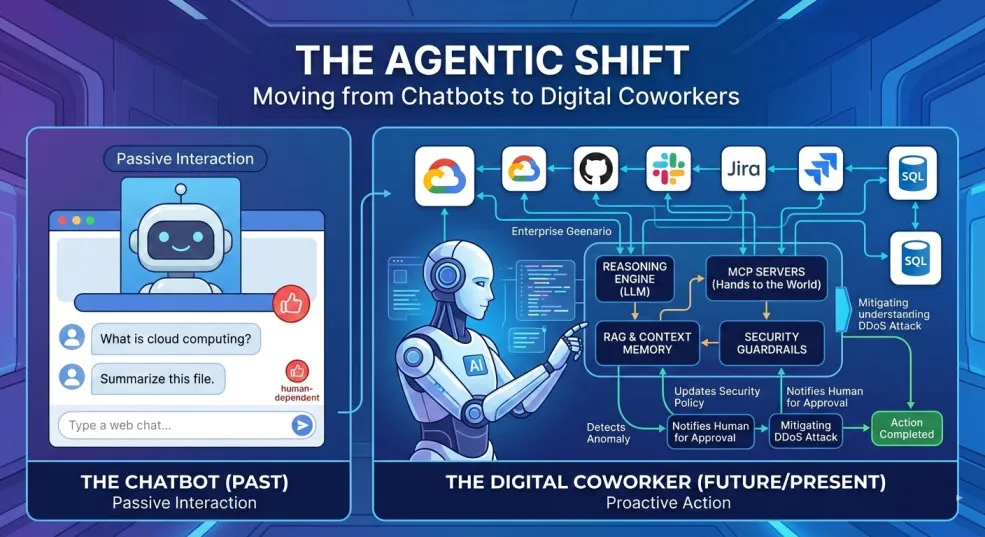
The Agentic Shift: Moving from Chatbots to Digital Coworkers
By 2026, enterprises are moving from AI chatbots that answer questions to digital coworkers that own outcomes across end-to-end workflows.

The Future of Agentic AI in Enterprise Applications
Why the next 3–6 months will define enterprise AI leadership — and how product and technology leaders can prepare for agentic systems that plan, decide, orchestrate, and execute.

Navigating the Future of AI Agents: MCP vs. A2A vs. ACP vs. ANP
A practical breakdown of the 4 key protocols shaping interoperable AI agents—what they do, where they fit, and how to choose (MCP, A2A, ACP, ANP).

AI 101: Your Gateway to the World of Large Language Models
A practical, non-fluffy guide to AI and Large Language Models (LLMs) for developers, CXOs, and AI leaders—what they are, how they work, when to use which model, and how to get reliable answers.

Google Maps for Your Code: Rescuing Architecture with the C4 Model
How the C4 model turns messy architecture diagrams into a clear, zoomable map of your systems—so teams can align, migrate, and evolve faster.
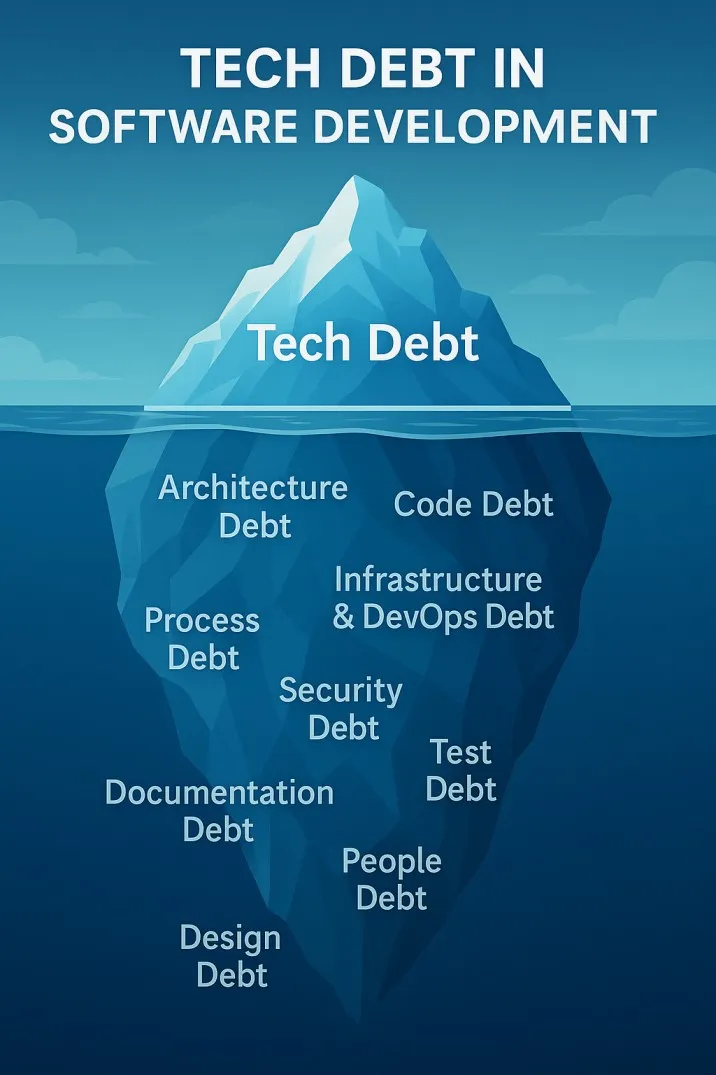
The Iceberg Beneath Your Code: Understanding Tech Debt in Software Development
Tech debt is the hidden iceberg beneath your codebase—slowing teams, inflating risk, and threatening outages. Here’s how to see it clearly and pay it down strategically.
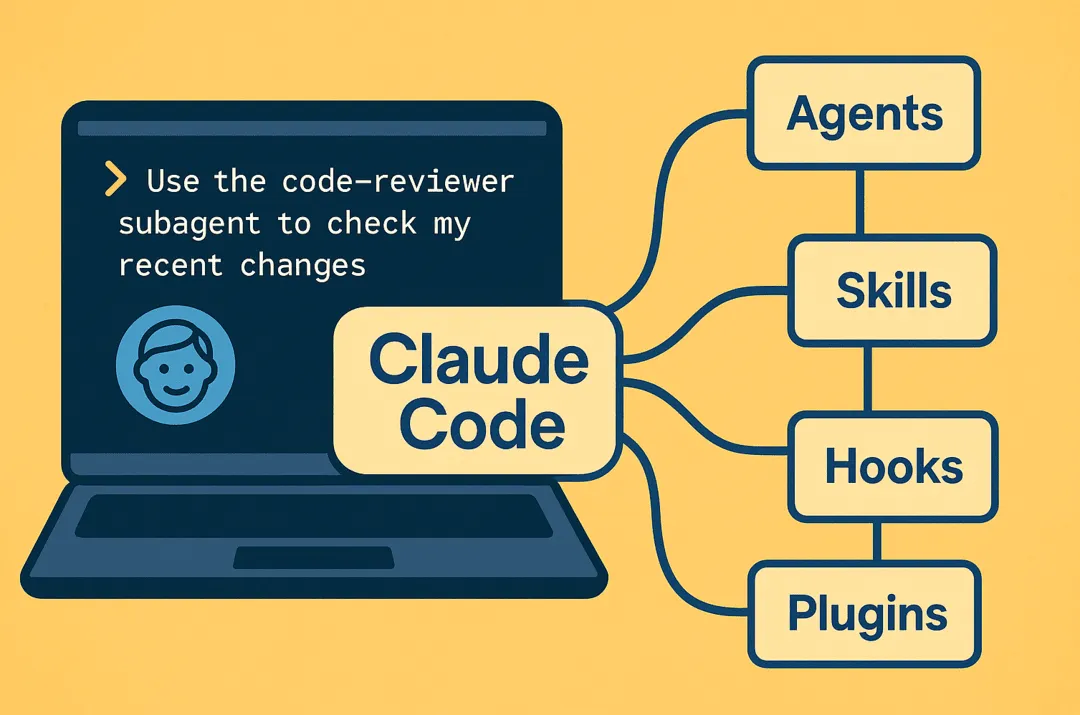
How Claude Code Turns Your Terminal into an Agentic Dev Team
Claude Code is a framework for composing terminal-native AI agents with subagents, skills, hooks, and plugins to automate real dev workflows with control and determinism.



