Zero Trust Security: An Enterprise Strategy for Security That Never Sleeps
“In the digital enterprise, trust is not a perimeter — it’s a strategy.”
The New Security Reality: Why Perimeters Have Failed
In the past, security revolved around a simple idea — build strong walls around the castle, and everything inside is trusted. Firewalls guarded the perimeter, VPNs created safe tunnels, and employees operated from within.
But today, that world no longer exists. Cloud adoption, SaaS sprawl, and remote work have erased the perimeter. Employees connect from anywhere, workloads run across multiple clouds, and third-party APIs exchange sensitive data continuously.
The results are visible in the headlines:
- Capital One (2019) — a misconfigured AWS role exposed 100 million credit applications.
- SolarWinds (2020) — a trusted vendor’s software update became a global supply chain compromise.
- Okta (2023) — unauthorized access to support systems caused downstream customer exposure.
These breaches weren’t about weak firewalls — they were about over-trusting systems, credentials, and networks.
The lesson: implicit trust is the biggest vulnerability in the cloud age.
This is where Zero Trust Security Architecture (ZTSA) emerges — not as a tool, but as a strategic operating model for digital security.
What Is Zero Trust Security Architecture (ZTSA)?
Zero Trust is built on one powerful idea:
“Never trust, always verify.”
The Strategic Pillars of Zero Trust
- Identity – Every entity (human or machine) must be authenticated and authorized.
- Device – Only compliant, secure devices gain access.
- Network – Micro-segmented zones limit lateral movement.
- Application & Workload – Policy-based access and continuous monitoring.
- Data – Classified, encrypted, and access-controlled.
- Visibility & Analytics – Real-time insights to detect anomalies.
- Automation & Orchestration – Policy enforcement and incident response at scale.

Zero Trust isn’t a product you buy — it’s a strategic framework that reshapes how enterprises think, design, and operate secure systems.
Why Enterprises Need Zero Trust in the Cloud
Modern enterprises face three converging realities:
- Cloud-first ecosystems: Data moves across AWS, Azure, and GCP daily.
- Workforce anywhere: Remote and hybrid teams rely on internet-based access.
- Evolving threat surface: APIs, containers, and SaaS expand exposure exponentially.
Without Zero Trust, enterprises face:
- Inconsistent access policies across environments.
- Over-permissive IAM roles.
- Inadequate visibility of east-west traffic.
- Increased insider threat exposure.
A single compromised credential or unverified API call can pivot across environments in seconds — Zero Trust stops this lateral movement by enforcing context-based verification at every step.
The Business Case for Zero Trust
For CXOs, Zero Trust isn’t just a security upgrade — it’s a business enabler.
Strategic Benefits:
- 🔒 Stronger protection of sensitive data.
- ⚙️ Seamless compliance with GDPR, ISO 27001, SOC 2, and HIPAA.
- 🌐 Consistent policy enforcement across multi-cloud.
- 🚀 Accelerated digital transformation without compromising risk posture.
- 💡 Enhanced customer trust and brand resilience.
Enterprises embracing Zero Trust are proactively reducing risk, cutting incident response times, and achieving measurable resilience.
For example:
- A global bank implementing Zero Trust reduced lateral movement by 90% during red-team exercises.
- A telecom operator improved compliance audit turnaround by 40%.
- A SaaS enterprise cut breach detection time from 72 hours to under 30 minutes.
Strategic Challenges and Trade-offs
Like any transformation, Zero Trust comes with hurdles:
- Cultural resistance — security teams, developers, and operations must shift from “trust by default” to “verify every time.”
- Legacy integration — aging infrastructure and monolithic apps resist identity-based access control.
- Performance overhead — real-time verification may initially introduce latency.
- Vendor complexity — the market is flooded with “Zero Trust” tools with fragmented coverage.
- Investment alignment — it’s a journey requiring staged investments across people, process, and technology.
These are not reasons to delay — but signals to approach Zero Trust as a phased enterprise program, not a one-time project.
The Strategic Roadmap to Implement Zero Trust
Building a Zero Trust enterprise requires a clear strategy and phased execution. Here’s a five-stage enterprise roadmap:
Stage 1: Assess and Discover
- Map users, applications, devices, data, and cloud environments.
- Identify implicit trust paths and shadow access.
- Evaluate current maturity using frameworks like CISA’s Zero Trust Maturity Model or NIST 800-207.
Stage 2: Establish Identity as the New Perimeter
- Centralize identities via SSO and MFA across on-prem and cloud.
- Implement identity federation for all apps (workforce + third-party).
- Introduce conditional access and adaptive policies.
Stage 3: Secure the Network and Workloads
- Adopt micro-segmentation and context-aware access controls.
- Enforce least-privilege network access — e.g., AWS Verified Access, Azure Private Link, or GCP BeyondCorp.
- Inspect east-west traffic using CNAPPs, CSPMs, and EDR/XDR tools.
Stage 4: Protect Data Everywhere
- Implement data classification and encryption policies.
- Apply data loss prevention (DLP) and tokenization for sensitive workloads.
- Align access with “need to know” and “least privilege” principles.
Stage 5: Automate and Continuously Improve
- Centralize visibility with SIEM + SOAR integration.
- Automate response to identity anomalies, policy drift, or unapproved access.
- Continuously monitor KPIs and adjust trust policies using analytics and AI.
Governance and Operating Model
A successful Zero Trust strategy demands strong governance and a defined operating model.
Key Elements:
- Executive sponsorship — align with CIO/CISO strategic goals.
- Cross-functional ownership — Security, IT, CloudOps, DevSecOps, and Compliance.
- Policy governance board — defines trust rules, identity standards, and risk tolerances.
- Continuous training & awareness — make Zero Trust part of organizational DNA.
Governance ensures that Zero Trust isn’t just a technical deployment, but an enterprise-wide behavior model.
Measuring Success and Maturity
Measurement is critical to sustaining investment and trust from leadership.
Zero Trust Maturity Levels
- Initial – Siloed identity, implicit trust.
- Managed – MFA, basic identity control, limited segmentation.
- Defined – Policy-driven access, continuous monitoring.
- Adaptive – Contextual risk-based enforcement.
- Autonomous – AI-driven dynamic trust decisions.
Success Metrics
- % of users and devices under continuous verification.
- % of applications behind policy-enforced gateways.
- Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR).
- Reduction in unauthorized access incidents.
- Compliance audit pass rate and SLA adherence.
Regular maturity reviews help identify new investment areas and demonstrate tangible risk reduction.
Assessing Enterprise Readiness
Before beginning, enterprises should perform a Zero Trust Readiness Assessment:
- Identity and Access Management maturity.
- Cloud visibility and policy enforcement level.
- Endpoint posture validation capabilities.
- Data protection and classification frameworks.
- Monitoring and automation coverage.
You can benchmark using:
- CISA Zero Trust Maturity Model
- Microsoft Zero Trust Assessment Tool
- NIST SP 800-207 reference architecture
The goal is to find your “current trust posture” and define a north star vision for transformation.
The Strategic Endgame: Continuous, Intelligent Trust
Zero Trust is not a destination — it’s a living strategy. As cloud, AI, and automation reshape the enterprise, so must our definition of trust.
The organizations that succeed will be those that:
- Treat security as a strategic enabler, not a constraint.
- Continuously verify identity and behavior in every interaction.
- Align technology choices with business and risk objectives.
- View Zero Trust as a culture, not a control.
Because in the modern enterprise, trust must be earned — every time.
Final Thought
Zero Trust isn’t about distrusting your people or technology — it’s about trusting intelligently, guided by evidence, context, and automation.
It’s how future-ready enterprises will protect what matters most — their data, their reputation, and their customers’ trust.
Recent Posts
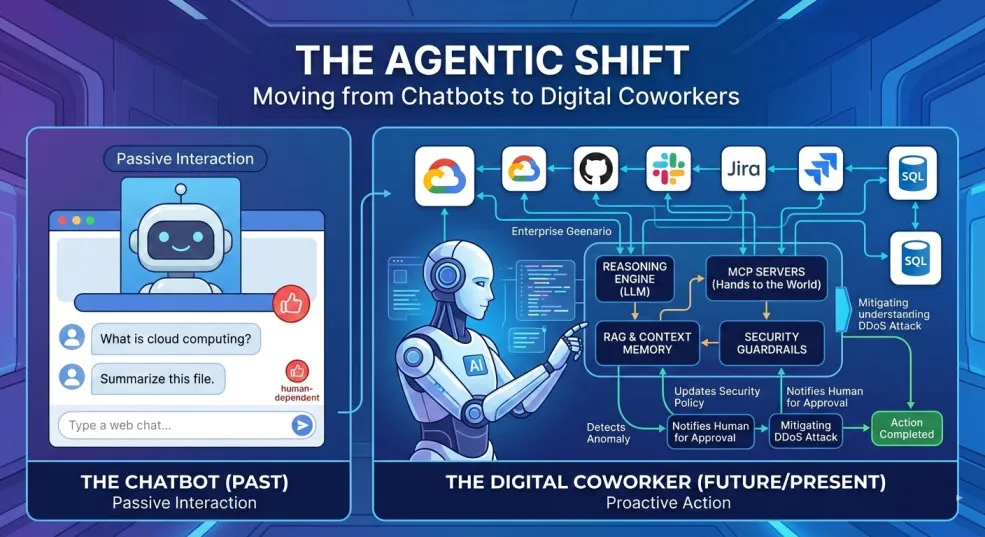
The Agentic Shift: Moving from Chatbots to Digital Coworkers
By 2026, enterprises are moving from AI chatbots that answer questions to digital coworkers that own outcomes across end-to-end workflows.

The Future of Agentic AI in Enterprise Applications
Why the next 3–6 months will define enterprise AI leadership — and how product and technology leaders can prepare for agentic systems that plan, decide, orchestrate, and execute.

Integration Modernization: An Enterprise Strategy for the Connected Enterprise
A Strategic framework for CIOs, CTOs, and enterprise architects to modernize integration, reduce risk, and unlock connected enterprise velocity.

Navigating the Future of AI Agents: MCP vs. A2A vs. ACP vs. ANP
A practical breakdown of the 4 key protocols shaping interoperable AI agents—what they do, where they fit, and how to choose (MCP, A2A, ACP, ANP).

AI 101: Your Gateway to the World of Large Language Models
A practical, non-fluffy guide to AI and Large Language Models (LLMs) for developers, CXOs, and AI leaders—what they are, how they work, when to use which model, and how to get reliable answers.

Google Maps for Your Code: Rescuing Architecture with the C4 Model
How the C4 model turns messy architecture diagrams into a clear, zoomable map of your systems—so teams can align, migrate, and evolve faster.
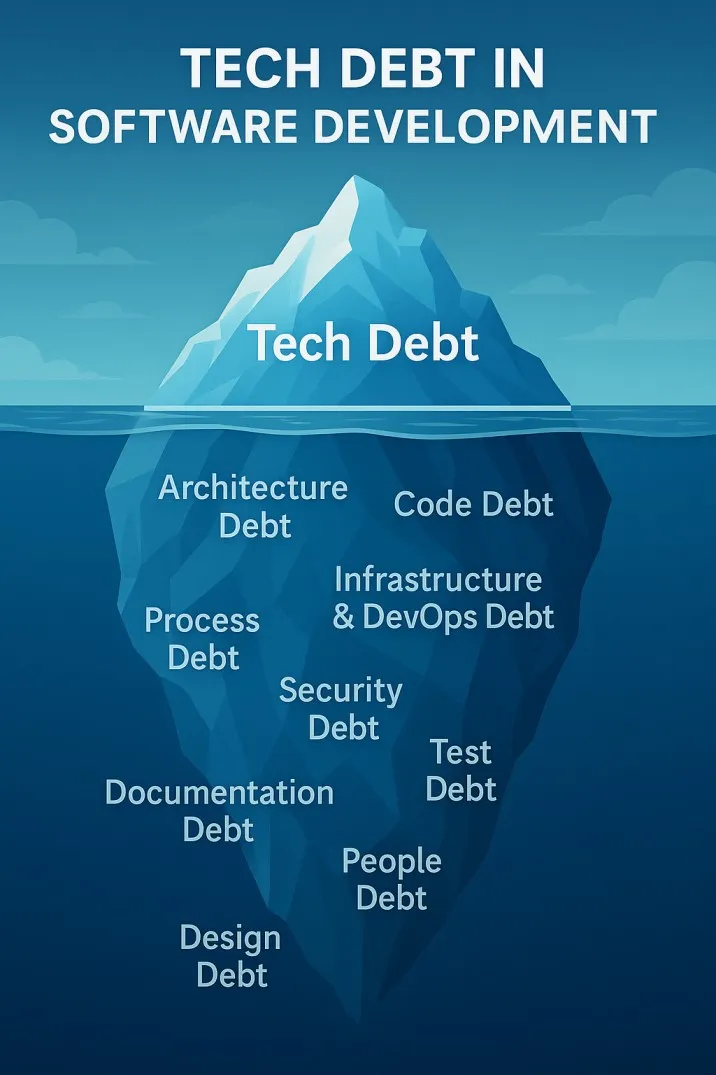
The Iceberg Beneath Your Code: Understanding Tech Debt in Software Development
Tech debt is the hidden iceberg beneath your codebase—slowing teams, inflating risk, and threatening outages. Here’s how to see it clearly and pay it down strategically.



